Click here to listen to the Audio version of this story!
Stand on a lease road in West Texas long enough and you will eventually see the entire history of the oilfield in one glance: a decades-old pumpjack still stroking, newer equipment tied into older flowlines, temporary gear staged for the next job, and, somewhere beyond the horizon, infrastructure that only a handful of people remember exists. Much of it still works. Almost none of it is pristine. Very little of it can simply be replaced.
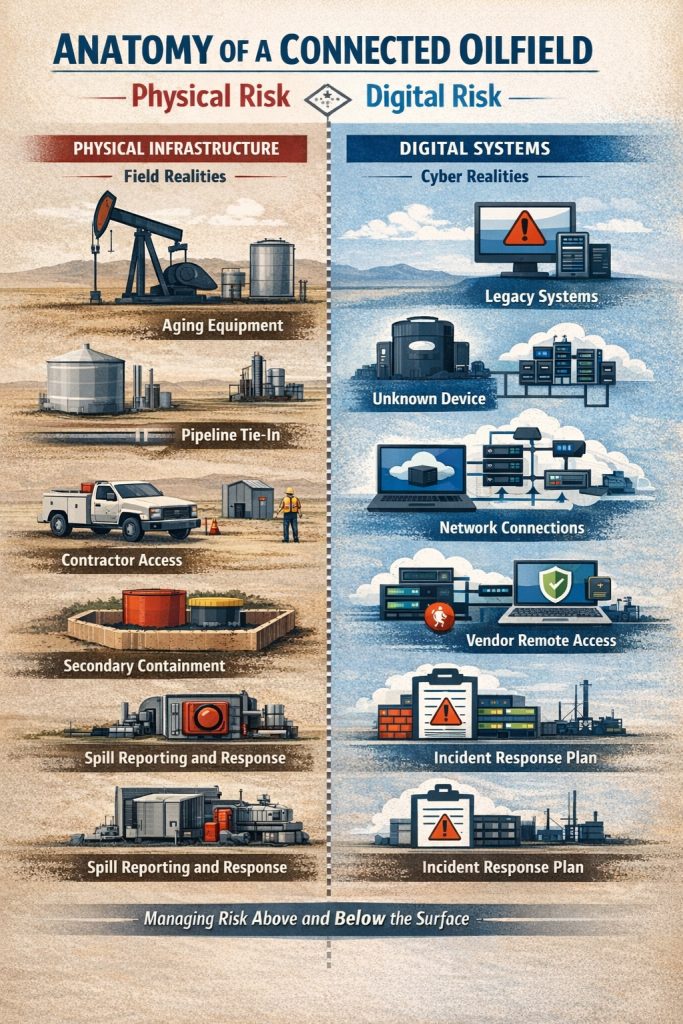
The modern cybersecurity landscape of the oil and gas industry looks remarkably similar.
In the oilfield, cybersecurity problems don’t resemble IT problems. They resemble oilfield problems. More pointedly, digital risk behaves like physical infrastructure that is aging, distributed, improvised, and rarely fully fixable.
And, as with physical risk, the consequences are real. Operational shutdowns, loss of critical data, and ransom scenarios are no longer theoretical. “The dangers are real,” says Justin Stephenson, founder of Midland-based consultancy Base Layer Technology LLC. “Operational shutdown, exfiltration of data, encryption of data, ransom situations. These need to be defended against.”
Assumptions vs. Reality
Physical corollary: On paper, every facility looks like a neat rectangle with a fence, a gate, and a tidy label. In the field, that rectangle dissolves into cattle guards, caliche roads, shared easements, handshake agreements from three operators ago, and a gate that’s either chained shut or hanging open depending on who came through last. There is always a back way in. There is always a tie-in nobody quite remembers approving. What was once temporary becomes permanent by sheer inertia.
For years, industrial control environments relied on the belief that isolation meant safety. Systems were local, connectivity was limited, and separation functioned as a protective barrier.
That assumption has eroded as remote operations, analytics, and digital optimization have become essential to competitiveness.
“The most dangerous misconception is that air-gapped operational systems are inherently safe,” says Daniel Crespo, a cybersecurity and industrial digital infrastructure leader at Chevron. “Remote monitoring, vendor access, and IT/OT convergence have quietly erased true isolation.”
The 2021 Colonial Pipeline incident made this shift visible. The company halted pipeline operations after a ransomware attack compromised business systems, illustrating that cyber events can force physical shutdowns even without direct manipulation of industrial controls. (U.S. Department of Energy; CISA)
Cybersecurity became an operational concern the moment digital disruptions could stop production.
Connectivity as the New Gathering System
Physical corollary: Tie-ins are the circulatory system of the oilfield. One well feeds a battery, which feeds a line, which feeds a system that disappears over the horizon. Efficiency improves with every connection, but so does the potential for trouble to travel. A slug, a pressure spike, or a contaminant introduced miles away can show up at your facility uninvited and fully committed. Once systems are connected, you inherit not just the benefits, but the problems.
Digital connectivity functions the same way. SCADA systems, cloud platforms, and remote support links connect facilities across vast distances, improving performance while expanding exposure.
Third-party access is often necessary to maintain equipment and software, but it also extends the operational boundary beyond company walls.
“One compromised vendor can ripple across multiple facilities,” Daniel Crespo notes.
Regulators now treat this as a critical infrastructure issue. In the aftermath of the Colonial incident, federal directives required pipeline operators to report cyber incidents and strengthen cybersecurity coordination and planning. (TSA Pipeline Security Directives)
Connectivity is no longer optional, but neither is managing the risk that travels with it.
Legacy Systems: Still Producing, Still Vulnerable
Physical corollary: The Permian Basin is a museum that still pays dividends. Equipment built when disco was a viable career path continues to move product today. Nobody replaces a producing asset just because it’s old; they nurse it, retrofit it, brace it, and occasionally whisper threats at it. Replacement means downtime, cost, and uncertainty. So, the field does what it has always done: keep it running safely enough to justify another day of production.
Operational technology shares this longevity.
“Legacy systems were designed for uptime and reliability, not security,” Daniel Crespo explains. “Patching is often not an option.”
Instead, operators deploy layered controls around vulnerable systems. These include segmentation, strict access management, and continuous monitoring. International standards such as ISA/IEC 62443 emphasize lifecycle security practices tailored to industrial environments rather than wholesale replacement. (International Society of Automation)
This mirrors physical risk management. Secondary containment does not remove the possibility of a spill. It limits the damage.
Stephenson adds a financial dimension to this reality. “You’re going to spend the money anyway,” he says. “Either on the front end with training, systems, and upgrades, or on the back end after a catastrophic incident. Ransom, shutdown, recovery, hardening.”
The Visibility Problem: Physical and Digital
 Physical corollary: Every operator has a story about the asset nobody thought about until it mattered. The abandoned well hidden behind mesquite. The undocumented line discovered by a backhoe. The tank battery so remote it feels like it belongs to another county. Out of sight does not mean out of service. It just means the surprise will be bigger when something goes wrong.
Physical corollary: Every operator has a story about the asset nobody thought about until it mattered. The abandoned well hidden behind mesquite. The undocumented line discovered by a backhoe. The tank battery so remote it feels like it belongs to another county. Out of sight does not mean out of service. It just means the surprise will be bigger when something goes wrong.
Digitally, unknown devices, undocumented interfaces, or lingering access pathways create similar blind spots.
“You can’t protect what you don’t know exists,” Daniel Crespo says. “Build an OT asset inventory and map every remote access path.”
For smaller operators and service companies, maintaining visibility can be particularly challenging as equipment moves between locations and responsibilities shift. Stephenson advises a disciplined approach. Continuous monitoring, asset inventory, and formal risk assessment should be supported by coordination between technical teams, HR, and executive leadership to implement policies.
Learning from incidents across the industry is equally important. “Don’t let a good tragedy go to waste,” he says. Organizations that study failures elsewhere can strengthen defenses before experiencing one themselves.
The Human Layer
Physical corollary: The oilfield runs on procedures written in ink and interpreted in dust. You can engineer the safest system imaginable, but it still depends on people remembering the checklist at three in the morning in 20-mile-per-hour wind. Most incidents are not caused by equipment spontaneously developing bad intentions. They happen because someone skipped a step, misunderstood a condition, or assumed someone else had it handled.
Cybersecurity follows the same pattern.
“The human element remains the most underinvested layer of defense,” Daniel Crespo emphasizes. Social engineering, credential misuse, and insider actions frequently serve as entry points into operational environments.
Governance, including who has access, how decisions are made, and how policies are enforced, often determines outcomes more than technical tools.
Stephenson underscores that cybersecurity must align with broader business objectives. IT and OT cannot operate as isolated technical functions. They must support operational goals, financial priorities, and organizational risk tolerance.
“IT/OT must align with business goals,” he says.
Continuity Under Constraint
Physical corollary: The oilfield does not wait for perfect conditions. Work proceeds through heat, cold, shortages, delays, and equipment that behaves like it has opinions. Plans are written not to eliminate uncertainty, but to survive it. When something fails, the question is not whether operations stop forever. It is how quickly control can be regained without making things worse.
Cybersecurity strategy reflects the same mindset.
Facilities cannot be taken offline casually for upgrades, and threats cannot be eliminated entirely. Organizations must determine what level of risk they are willing to accept and how to mitigate it.
“There are always going to be attacks,” Stephenson notes. “It becomes a question of risk mitigation and what level of risk you’re willing to accept.”
This perspective is increasingly embedded in regulatory expectations as well. Current pipeline directives require operators to maintain incident response plans designed to limit operational disruption and restore control quickly if an event occurs. (TSA)
The objective is straightforward. Maintain safe operations even when systems are under stress.
The Cost of Inaction
Physical corollary: Deferred maintenance is a loan shark. It offers relief today and collects with interest later. A small leak becomes a rupture. A vibration becomes a failure. Eventually the bill arrives, and it is never itemized in your favor.
Cybersecurity investments follow the same pattern.
“There’s the cost of systems and upgrades,” Stephenson says, “but the price for not investing is operational, reputational, and financial.”
The threat environment has also evolved dramatically. Decades ago, limited connectivity constrained both operations and attackers. Today’s high-speed networks provide unprecedented capability for legitimate activity and malicious intrusion alike.
“A firewall and antivirus aren’t going to cut it anymore,” Stephenson explains. “The technology evolved. The pipe for threats is huge now.”
Familiar Kind of Risk
Physical corollary: The oilfield has always been a sprawling, improvised system held together by engineering, experience, and a stubborn refusal to quit. Thousands of assets, multiple owners, incomplete information, and real consequences when something goes wrong. It works not because it is simple, but because the people operating it understand its complexity.
Cyber risk is the same problem expressed through digital systems.
Industrial control technologies now sit at the intersection of physical infrastructure and global connectivity, governing production, transport, and processing. As these systems evolve, so do the risks.
The industry has never relied on perfection. Reliability comes from layered safeguards, disciplined operations, and experienced judgment applied over time.
Cybersecurity extends that philosophy into software and networks.
The vulnerabilities facing modern energy operations are not foreign intrusions into an otherwise stable system. They are the digital reflection of the oilfield’s enduring realities: aging assets, interconnected infrastructure, human decision-making, economic constraints, and the constant need to keep energy flowing safely.
Managing those risks is not a one-time project.
It is simply part of operating the modern oilfield.
Christian Lombardini, a former field operator and manager, is now a communications and content consultant for oil & gas companies and creators. You can find Christian and his The Oilfield Leader Podcast on LinkedIn.











Leave a Reply